At least 11 "government-backed" hacking groups have exploited a previously unknown zero-day vulnerability in Windows to steal data and conduct cyber espionage, according to Trend Micro's Zero Day Initiative (ZDI).
Researchers discovered the bug last year, but in late September 2024, Microsoft marked the issue as "non-compliant" and said it would not release patches to fix it.
"We found about a thousand Shell Link (.lnk) samples exploiting ZDI-CAN-25373. The total number of exploitation attempts is likely much higher," the researchers wrote. "We subsequently submitted a proof-of-concept exploit to Microsoft via the Trend ZDI bug bounty program, but they refused to patch the vulnerability with a security update."
The issue has not yet been assigned a CVE identifier, but Trend Micro is tracking it as ZDI-CAN-25373 . According to experts, the vulnerability allows attackers to execute arbitrary code on systems running Windows.
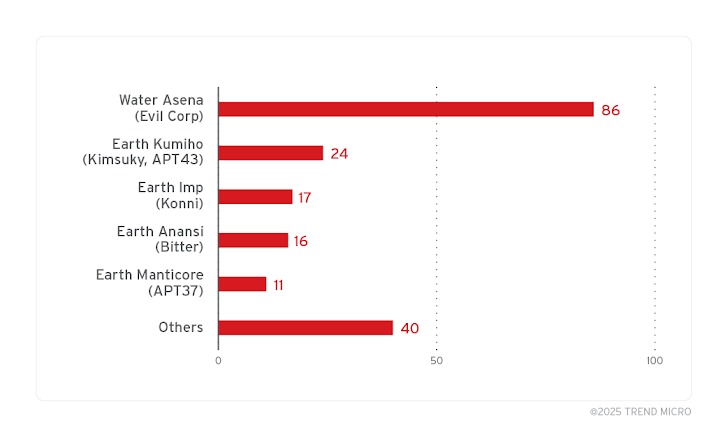
At the same time, the analysis showed that ZDI-CAN-25373 has long been used in attacks by groups such as Evil Corp, APT43 (Kimsuky), Bitter, APT37, Mustang Panda, SideWinder, RedHotel, Konni, and so on.
These attacks mainly targeted users from North America, South America, Europe, East Asia, Australia, and other countries. Of all the attacks studied, almost 70% were related to espionage and information theft, and only 20% of the attacks were aimed at financial gain.
“These campaigns used a variety of payloads and malware loaders, including Ursnif, Gh0st RAT, and Trickbot, and MaaS platforms make it even more difficult to piece together the full threat landscape,” Trend Micro said .
ZDI-CAN-25373 is a Critical User Interface Corruption (CWE-451) issue. The bug allows .lnk files in Windows to be used to evade detection and execute code on vulnerable devices without the user's knowledge.
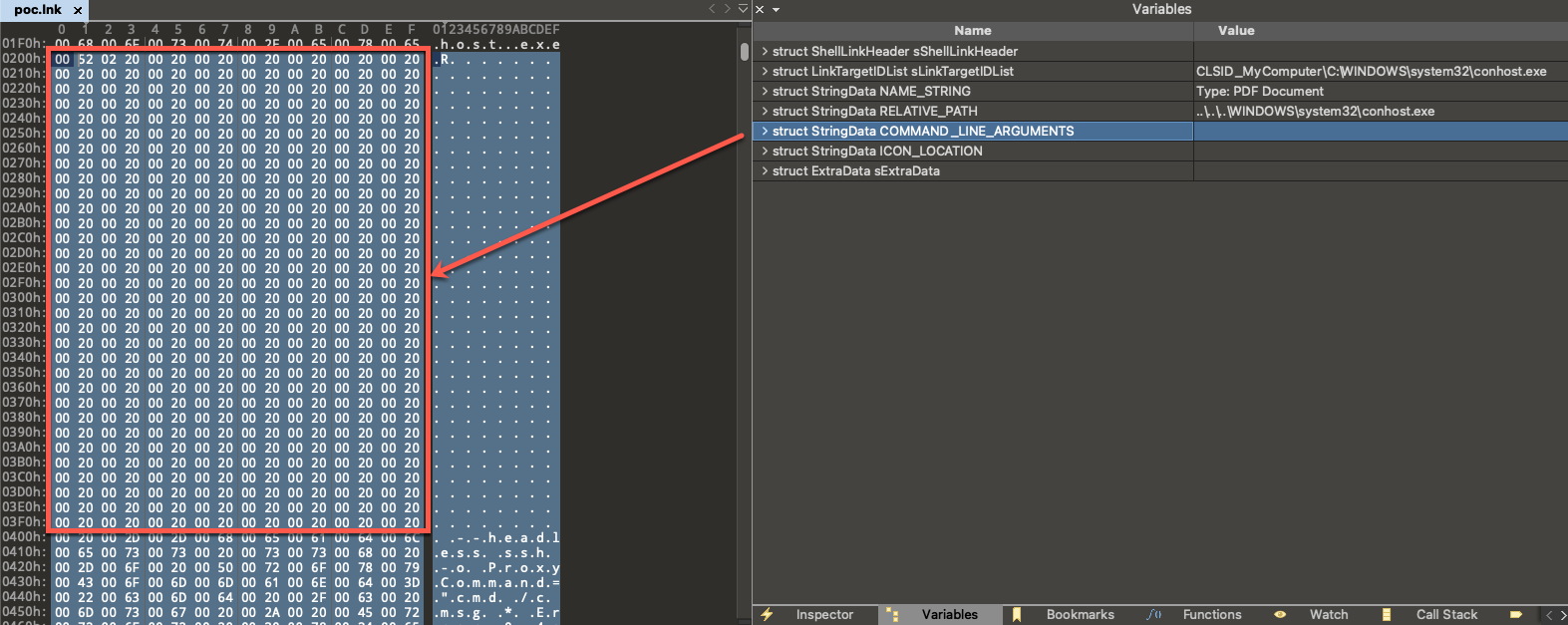
Hackers typically exploit ZDI-CAN-25373 by hiding malicious command line arguments in .lnk files using whitespace characters added to the COMMAND_LINE_ARGUMENTS structure.
According to the researchers, such whitespace characters can be represented in different forms: as hexadecimal representations of a space (\x20), horizontal tab (\x09), line feed (\x0A), vertical tab (\x0B), form feed (\x0C), and carriage return (\x0D).
As a result, if a Windows user views such a .lnk file, the malicious arguments are not displayed in the Windows user interface due to the added whitespace characters, and the command line arguments added by the attackers remain hidden from prying eyes.
"Exploitation of this vulnerability requires user interaction, as the target must visit a malicious page or open a malicious file," Trend Micro said. "Pre-crafted data in the .lnk file could cause the malicious content in the file to be invisible to a user viewing the file through the Windows user interface. An attacker could use this vulnerability to execute code in the context of the current user."
Following the publication of Trend Micro's report, Microsoft representatives told the media that the company was still considering the possibility of fixing this vulnerability in the future.
"We appreciate the work of ZDI in submitting this report as part of a coordinated disclosure of vulnerabilities. Microsoft Defender has detection and blocking capabilities for this threat, and Smart App Control provides an additional layer of protection by blocking malicious files from the internet. As a security best practice, we recommend that users exercise caution when downloading files from unknown sources, as outlined in the security alerts that are designed to recognize and warn users about potentially dangerous files. While the user experience issues described in the report do not meet our criteria for an immediate fix, we will consider addressing these issues in a future release," Microsoft said .