Kaspersky Lab specialists have identified a new scheme for distributing the Arcane stealer. Attackers have created a downloader called ArcanaLoader, which is supposedly needed to download popular cheats for games (for example, for Minecraft), but in fact it infects devices with malware. Most of the attacked users are located in Russia, Belarus, and Kazakhstan.
According to researchers, an unknown hack group began distributing Arcane by posting ads on YouTube. The description under the video included a link to an archive supposedly containing cheats, which in fact contained a stealer.
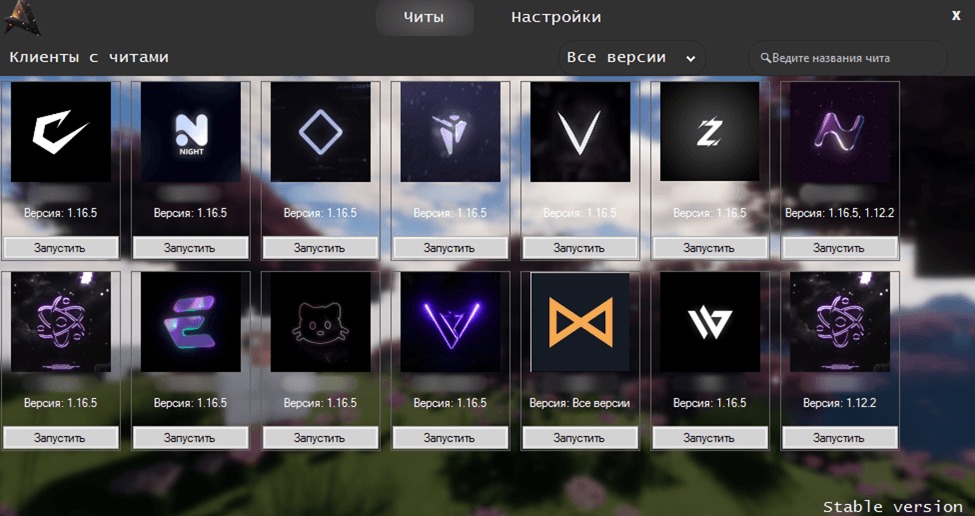
At the end of 2024, the attackers improved this scheme. Now they advertise not an archive, but the ArcanaLoader loader. This loader with a graphical interface is supposedly necessary for downloading popular cheats, cracks and other similar software. After it is launched, the Arcane infostealer penetrates the victim's device.
It is noted that the attackers did not stop at developing the loader. In addition, they created a Discord server with channels where news about cheats, support, and links to download new versions of ArcanaLoader are published.
On one of the Discord channels, researchers found ads looking for bloggers for advertising on YouTube: they are supposed to add links to the uploader in the description under their videos. The attackers are looking for bloggers who have at least 600 subscribers, more than 1,500 views per video, and two videos with links. For advertising, performers are promised a new role on the server, access to some chats, and payment for high traffic.
The Arcane stealer was first discovered in late 2024. Much of its code is borrowed from other similar malware, but so far this threat has not been assigned to any known family.
Currently, the stealer can steal logins, passwords, and payment card data from Chromium and Gecko-based browsers from infected systems. In addition, Arcane collects system information, such as the user name and device, gets lists of running processes and Wi-Fi networks saved in the OS (as well as passwords for them), and takes screenshots.
Arcane allows hackers to access configuration files, settings information, and accounts for the following applications.
- VPN clients: OpenVPN, Mullvad, NordVPN, IPVanish, Surfshark, Proton, hidemy.name, PIA, CyberGhost, ExpressVPN.
- Network clients and utilities: ngrok, Playit, Cyberduck, FileZilla, DynDNS.
- Messengers: ICQ, Tox, Skype, Pidgin, Signal, Element, Discord, Telegram, Jabber, Viber.
- Email clients: Outlook.
- Game clients and services: Riot Client, Epic, Steam, Ubisoft Connect (former Uplay), Roblox, Battle.net, various Minecraft clients.
- Crypto wallets: Zcash, Armory, Bytecoin, Jaxx, Exodus, Ethereum, Electrum, Atomic, Guarda, Coinomi.
"Popular computer games attract the interest of not only gamers, but also attackers. In general, the methods of the latter are quite standard. However, we see that in the case of Arcane, the attackers have improved their tools, having started distributing the stealer not just in an archive: now they use a downloader with popular cheats as bait. In this way, the attackers sought to give the campaign more imaginary legitimacy," comments Oleg Kupreev, a cybersecurity expert at Kaspersky Lab.
Photo: Kaspersky Lab




