Microsoft has revealed that nearly 1 million Windows devices have been hit by a sophisticated malvertising campaign in recent months, stealing credentials, cryptocurrency and sensitive information from infected machines.
According to the researchers, the campaign began in December 2024, when unknown attackers began distributing links that loaded ads. Microsoft says the sites that hosted the ads were pirated streaming platforms with illegal content. The company's report names two such domains: movies7[.]net and 0123movie[.]art.
“Streaming sites were installing malicious redirectors to generate revenue from payment platforms for views or clicks,” the experts write.
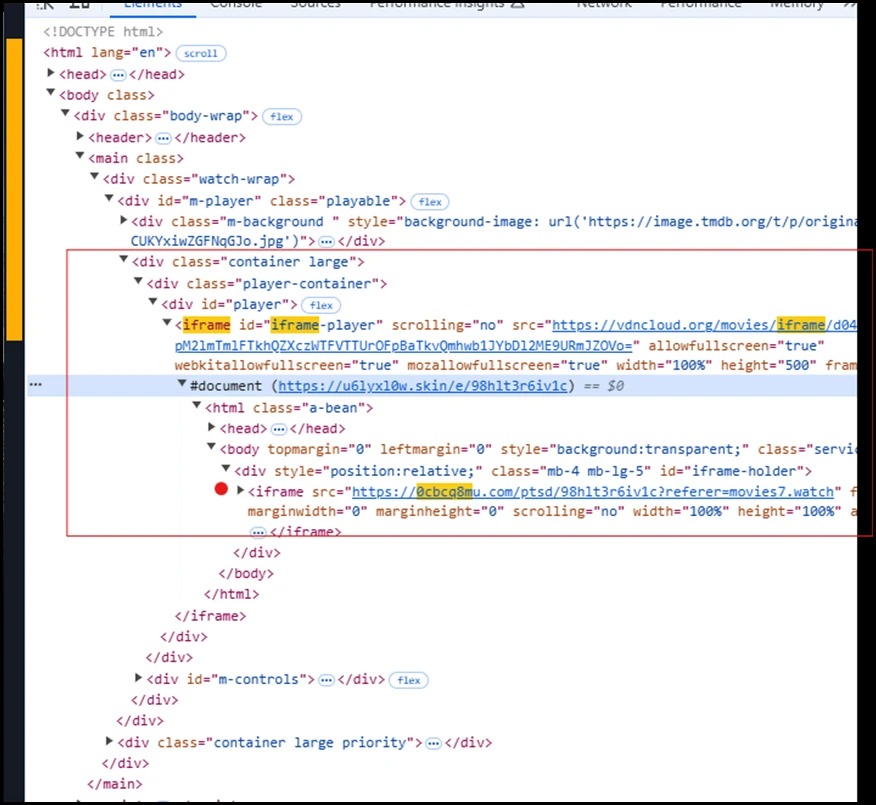
The malicious links embedded via iframes took victims through a chain of redirects, a series of intermediate sites (such as a scam tech support site), and ultimately led to GitHub repositories that hosted a range of malicious files.
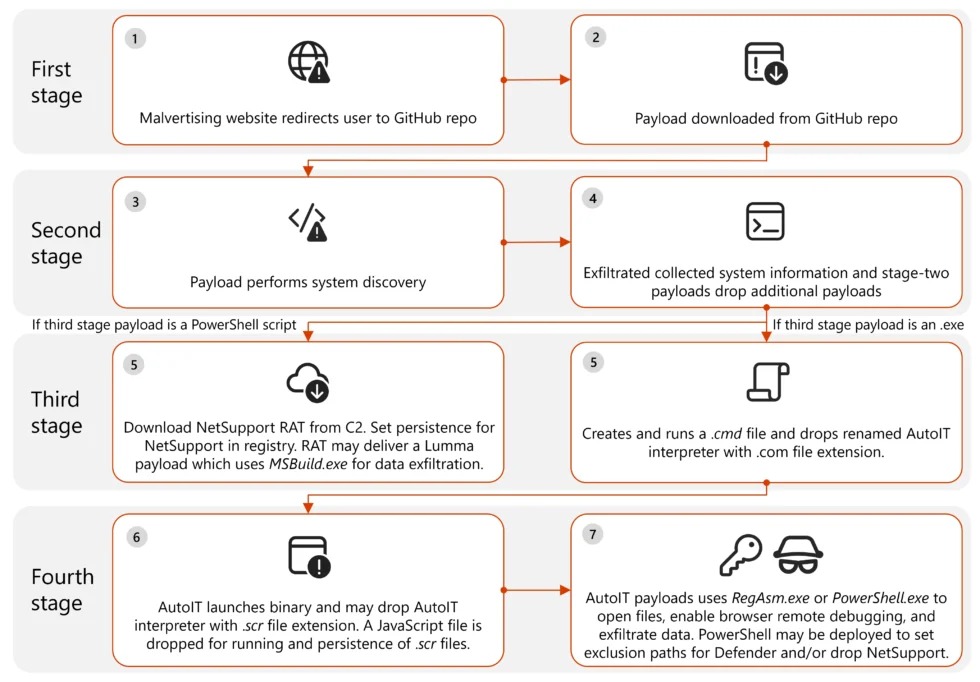
The malware was deployed in several stages. In the early stages, information about the user's device was collected, presumably to configure subsequent stages of the attack. In later stages, malware detection applications were disabled, a connection was established with the control servers, and the NetSupport malware was installed in the system.
“Depending on the second-stage payload, one or more executable files, and sometimes an encoded PowerShell script, were delivered to the infected device,” the researchers wrote. “These files triggered a chain of events that included command execution, payload delivery, defense evasion, persistence, C&C communications, and data theft.”
GitHub was primarily used to host the payload, but Discord and Dropbox were also used.
Experts believe that the campaign was opportunistic, meaning that the attackers attacked everyone without targeting specific people, organizations, or industries. It is noted that these attacks affected machines belonging to both individuals and various organizations.
The malware that penetrated the victims' systems (usually the Lumma stealer and the open source Doenerium stealer) stole the following data from browsers, where login cookies, passwords, histories, and other sensitive information could be stored.
- \AppData\Roaming\Mozilla\Firefox\Profiles\
.default-release\cookies.sqlite; - \AppData\Roaming\Mozilla\Firefox\Profiles\
.default-release\formhistory.sqlite; - \AppData\Roaming\Mozilla\Firefox\Profiles\
.default-release\key4.db; - \AppData\Roaming\Mozilla\Firefox\Profiles\
.default-release\logins.json; - \AppData\Local\Google\Chrome\User Data\Default\Web Data;
- \AppData\Local\Google\Chrome\User Data\Default\Login Data;
- \AppData\Local\Microsoft\Edge\User Data\Default\Login Data.
The attackers were also interested in files stored in the Microsoft OneDrive cloud service, and the malware checked for the presence of cryptocurrency wallets (Ledger Live, Trezor Suite, KeepKey, BCVault, OneKey and BitBox) on the victim’s machine.
According to Microsoft, the first stage payloads were digitally signed, and the company has now identified and revoked 12 different certificates used in these attacks.



